Discover the Power of LinkDaddy Cloud Services: Official Press Release Insights
Discover the Power of LinkDaddy Cloud Services: Official Press Release Insights
Blog Article
Secure and Efficient Data Monitoring Through Cloud Services
In the ever-evolving landscape of information management, the application of cloud solutions has actually emerged as a pivotal solution for companies seeking to fortify their information protection steps while streamlining operational efficiencies. universal cloud Service. The intricate interaction between safeguarding sensitive details and making sure smooth access postures a facility obstacle that organizations should navigate with diligence. By exploring the subtleties of safe and secure data management through cloud services, a deeper understanding of the techniques and innovations underpinning this standard change can be unveiled, clarifying the diverse advantages and factors to consider that shape the contemporary data monitoring community
Relevance of Cloud Services for Information Management
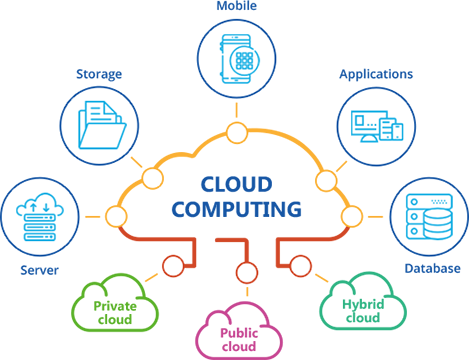
Cloud services play an important role in modern-day information monitoring methods due to their scalability, availability, and cost-effectiveness. Organizations can easily scale up or down their information storage space needs without the hassle of physical facilities expansion. This scalability permits services to adjust rapidly to altering information demands, making sure effective operations. Furthermore, cloud solutions provide high accessibility, making it possible for users to gain access to data from anywhere with an internet connection. This access advertises cooperation amongst teams, also those functioning remotely, leading to improved efficiency and decision-making procedures.
Moreover, cloud services use cost-effectiveness by removing the demand for spending in expensive hardware and upkeep. In essence, the importance of cloud solutions in data management can not be overemphasized, as they offer the necessary tools to improve operations, improve partnership, and drive company development.
Trick Safety And Security Challenges in Cloud Data Storage

To deal with these safety and security difficulties, organizations require robust safety and security actions, consisting of security, accessibility controls, regular safety audits, and team training. Partnering with relied on cloud provider that use advanced protection attributes and conformity qualifications can additionally help mitigate threats connected with cloud information storage. Inevitably, a proactive and extensive strategy to safety and security is crucial in securing data stored in the cloud.
Implementing Information Encryption in Cloud Solutions
Executing data encryption in cloud remedies includes using durable encryption formulas and secure vital monitoring practices. Security keys need to be stored independently from the encrypted data to include an additional layer of security. Furthermore, organizations should consistently upgrade file encryption secrets and employ strong accessibility controls to limit who can decrypt the information.
Additionally, information security need to be used not just during storage however additionally during information transmission to and from the cloud. Safe and secure interaction protocols like SSL/TLS can assist safeguard data en route, ensuring end-to-end security. By prioritizing data file encryption in cloud remedies, companies can bolster their data protection posture and maintain the confidentiality and integrity of their sensitive information.
Finest Practices for Data Backup and Recovery
Furthermore, carrying out routine healing drills is important to evaluate the performance of back-up procedures and the organization's capacity to restore information promptly. Automation of backup procedures can enhance operations and decrease the possibility for human mistake. File encryption of backed-up information includes an additional layer of safety and security, securing delicate information from unapproved accessibility throughout storage and transmission. By complying with these finest techniques, organizations can boost their information durability and guarantee seamless procedures when faced with unpredicted events.
Tracking and Auditing Information Gain Access To in Cloud
To preserve information honesty and safety within cloud settings, it is essential for companies to develop robust measures for surveillance and bookkeeping data gain access to. Tracking information gain access to includes tracking that accesses the data, when they do so, and what activities they carry out. By executing tracking systems, organizations can discover any kind of unauthorized gain access to or unusual activities quickly, enabling them to take prompt action to reduce potential threats. Bookkeeping data accessibility goes an action even more by providing an in-depth document of all information access activities. This audit trail is essential for conformity purposes, investigations, and identifying any patterns of questionable habits. Cloud service carriers frequently use devices and services that facilitate tracking and auditing of information accessibility, permitting companies to gain insights right into just how their data is being utilized and ensuring accountability. universal cloud Service. By actively checking and auditing information gain access to in the cloud, organizations can enhance their total protection pose and preserve control over their delicate info.
Final Thought
Finally, cloud solutions play an important role in ensuring reliable and protected information management for organizations. By resolving essential security challenges via information encryption, back-up, healing, and checking methods, organizations can click over here now protect sensitive information from unapproved gain access to and information violations. Applying these best methods in cloud services promotes data stability, privacy, and accessibility, ultimately boosting cooperation and productivity within the company.
The vital safety and security difficulties in cloud data storage revolve around data violations, data loss, conformity regulations, and information residency worries. By encrypting data before it is published to the cloud, organizations can minimize the risk of unapproved gain access to and data violations. By focusing on information file encryption in cloud solutions, companies can boost their information safety and security stance and preserve the privacy and stability of their delicate information.
To preserve information stability and safety and security within cloud environments, it is vital for organizations to establish robust steps for monitoring and auditing information accessibility. Cloud solution carriers commonly provide tools and services that promote monitoring and auditing of data gain access look at this website to, allowing companies to get insights into how their information is being made use of and ensuring liability.
Report this page